Cyber Shadows Over the US-Iran War: $10M Bounty Reveals Persistent Iranian APT Threat Mainstream Coverage Ignores
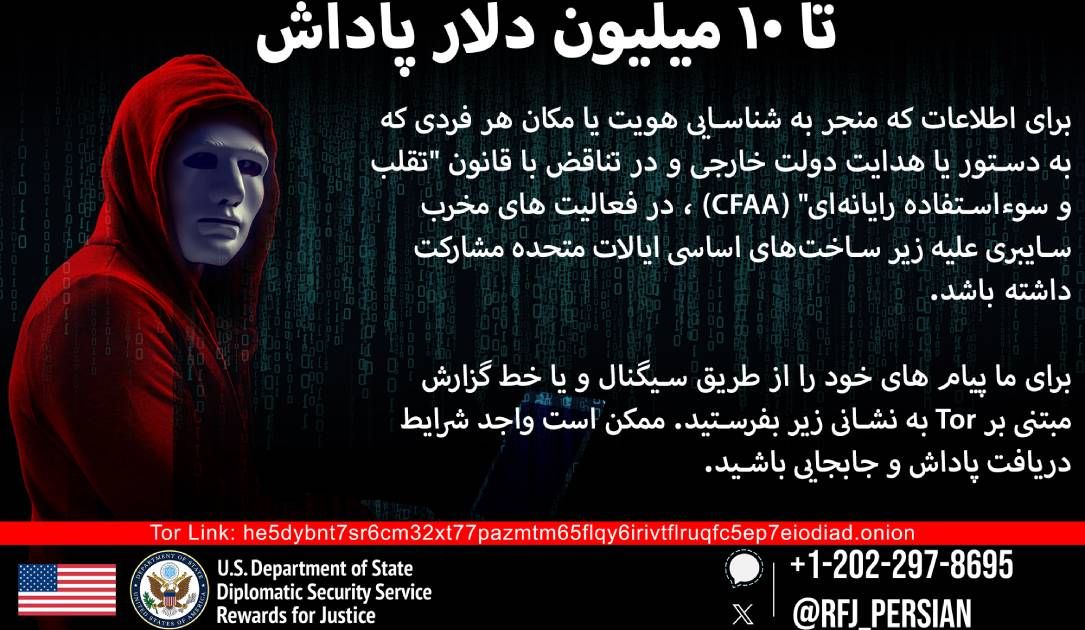
State Department reissues $10M bounty on Iranian hackers immediately after breach of Kash Patel’s email, exposing the underreported cyber front in active US-Iran hostilities and the limited success of prior US deterrence efforts.
The State Department's reissuance of a $10 million reward for information on Iranian cyber actors, timed just hours after the FBI confirmed a breach of Director Kash Patel’s personal email account, is not a routine bureaucratic update. It is a public signal that the cyber domain remains a live and increasingly dangerous front in the active US-Iran conflict. While cable news cycles obsess over kinetic exchanges, proxy militias, and missile intercepts, this bounty underscores a quieter, more persistent campaign that has been running in parallel for over a decade.
Original coverage in The Record correctly notes the timing but misses the deeper institutional pattern. This is not the first such reward. The US previously offered millions for the SamSam ransomware operators in 2018 and for members of the Mabna Institute in 2020 tied to intellectual property theft and election interference. The reissuance suggests those earlier efforts failed to meaningfully degrade Iranian capability. Groups tracked by Mandiant as APT33 (Elfin) and APT34 (OilRig), widely linked to the Islamic Revolutionary Guard Corps, have continuously refined their tactics—shifting from destructive wiper malware against Saudi targets in 2017 to sophisticated spear-phishing of US government officials and critical infrastructure operators today.
A 2023 CrowdStrike report on Iranian threat actors documented a notable uptick in credential harvesting and cloud service compromises aimed at US defense and law enforcement personnel, precisely the profile of the Patel breach. What mainstream kinetic-focused reporting consistently underplays is how these cyber operations serve as both intelligence collection platforms and coercive tools. In hybrid warfare doctrine favored by Tehran, cyber intrusions provide plausible deniability while creating leverage that can be activated during kinetic flare-ups. The targeting of personal email accounts of senior officials indicates a deliberate attempt to bypass hardened government networks and gather sensitive but unclassified insights into decision-making.
The bounty also reveals an uncomfortable truth about US defensive posture: despite billions spent on cyber defense, high-profile individuals remain vulnerable through basic opsec failures. Iranian operators have repeatedly exploited exactly this human layer, as seen in the 2021 Compromise of the Democratic Senatorial Campaign Committee and ongoing attacks on US airports and hospitals documented by the FBI and CISA. By offering rewards rather than solely relying on sanctions or indictments, the State Department is effectively crowdsourcing intelligence on these actors, acknowledging that technical attribution alone has not produced sufficient disruption.
This cyber dimension carries escalation risks that are harder to manage than missile volleys. A successful breach of energy sector systems or transportation networks could produce effects indistinguishable from sabotage without ever firing a shot. As tensions remain elevated, Iranian cyber units are likely positioned to conduct disruptive operations calibrated to stay below the threshold of declared war while imposing real costs. The $10M bounty is less about catching individual hackers than it is about publicly acknowledging that the cyber war is already underway and that the United States is still struggling to deter it.
SENTINEL: Iranian cyber units are accelerating targeting of senior US officials’ personal accounts to gather intelligence and prepare disruptive options; expect coordinated cyber activity synchronized with any further kinetic exchanges in the coming months.
Sources (3)
- [1]State Department reissues $10 million reward for info on Iranian hackers(https://therecord.media/iran-hackers-state-department-reward)
- [2]Mandiant Intelligence Report: Iran’s Cyber Capabilities and APT33 Activity(https://www.mandiant.com/resources/reports/apt33-iranian-cyber-threat)
- [3]CrowdStrike 2023 Global Threat Report - Iranian Adversary Trends(https://www.crowdstrike.com/reports/2023-global-threat-report/)