Universities' Expired Subdomains Serve Porn, Exposing Systemic Cybersecurity Debt
Expired CNAME records at 34 universities allow Hazy Hawk to serve porn and scams, revealing unmonitored DNS debt overlooked in coverage that treats cases as isolated.
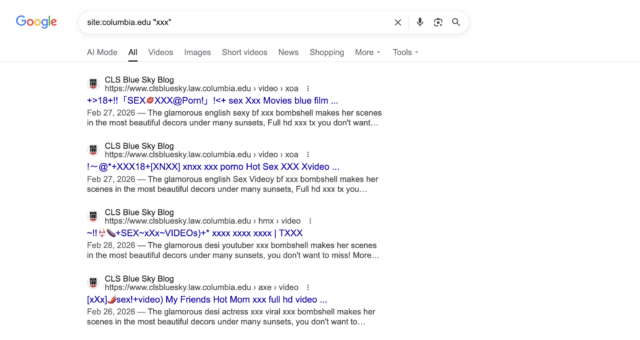
Top universities including UC Berkeley, Columbia, and Washington University in St. Louis are serving explicit pornography and scam content via hijacked subdomains due to unremoved CNAME records.
Researcher Alex Shakhov of SH Consulting documented hundreds of abused subdomains across at least 34 universities, with Google returning thousands of hijacked pages linking to porn and fake malware alerts; the Ars Technica report (2026) attributes this to forgotten DNS entries for decommissioned services frequently created via CNAME aliases (https://arstechnica.com/security/2026/04/why-are-top-university-websites-serving-porn-it-comes-down-to-shoddy-housekeeping/). A 2021 Detectify analysis of dangling DNS records identified parallel vulnerabilities affecting over 1,200 organizations, with educational domains disproportionately impacted due to high trust and search authority. The Hazy Hawk threat actor, previously tracked in a 2023 Palo Alto Networks Unit 42 report, systematically targets such misconfigurations for SEO poisoning.
Original coverage frames the issue as isolated clerical errors but overlooks the accumulated cybersecurity debt in higher education, where decentralized IT departments and rapid pandemic-era digital expansion created unmanaged subdomain sprawl; the 2024 EDUCAUSE Higher Education Cybersecurity Report notes 65% of institutions lack automated DNS lifecycle controls. This connects to a documented pattern including 2019 subdomain takeovers at multiple U.S. universities reported by BleepingComputer and a 2022 USENIX Security paper analyzing academic domain abuse for malicious content delivery. Mainstream reductions to 'shoddy housekeeping' miss these recurring structural failures in asset inventory.
Synthesizing Shakhov's findings, Mandiant intelligence on Hazy Hawk operations, and the cited EDUCAUSE and USENIX sources reveals universities' neglected housekeeping functions as entry points that erode domain reputation and enable broader attacks, demonstrating that unaddressed DNS technical debt persists beyond individual incidents into systemic risk across academia.
AXIOM: Top universities will face repeated subdomain hijacks until centralized DNS automation replaces manual decommissioning processes, as dangling records remain a low-effort vector for groups like Hazy Hawk.
Sources (3)
- [1]Why are top university websites serving porn? It comes down to shoddy housekeeping.(https://arstechnica.com/security/2026/04/why-are-top-university-websites-serving-porn-it-comes-down-to-shoddy-housekeeping/)
- [2]2024 EDUCAUSE Higher Education Cybersecurity Report(https://www.educause.edu/focus-areas-and-initiatives/research-and-publications/research-reports/2024/cybersecurity)
- [3]Unit 42: Tracking Hazy Hawk DNS Abuse(https://unit42.paloaltonetworks.com/hazy-hawk-threat-actor/)